
The term Ad-Hoc is a term with Latin roots and means "dedicated use". In most dictionaries, this phrase is given as meaning "for". Ad Hoc can be used to mean that it is a solution to a specific problem or issue and should not be considered as a default and permanent solution for use in future applications.

Ad Hoc network is one of the simplest implementations of topology or connection of wireless networks, in the usual case, the topologies of wireless computer networks are divided into two types: Infrastructure and Ad Hoc, in the Infrastructure type, a central device called We use Access Point as a point of connection to each other, and in fact, these Access Points act as a switch in wireless networks, in the second type of topology, which is called Ad Hoc, peripheral devices are no longer used, and each Some of the computers in this topology act as an Access Pint.
Ad hoc
networks usually have temporary and short-term applications and are not used for long-term applications. Unlike infrastructure networks, which have capabilities like LAN networks and can be assured of their stability, ad hoc networks have relatively low stability, and that is why they are used temporarily. By using this type of network, one or a group of computers that have a wireless network card can be connected to each other and exchange information.
The word Ad-Hoc has a Latin root and means "specific application". This term indicates that we use this type of service when it is not possible to use another type of service that is implemented publicly. Usually we use Ad-Hoc networks when it is not possible to use other types of networks. In Ad-Hoc communication, you establish a session and all devices are connected to that session, so with this method the access point will be practically removed. To create this session, one of the computers uses its wireless network card to create a domain name or rather an SSID like other access points, which can be identified for the frequency range in which other wireless network cards are active.
In this case, other computers can find the SSID of this network card by searching for other wireless networks and connect to it and start exchanging data. One of the limitations that can be mentioned for such wireless networks is the limited number of simultaneous connections to this network, which is why its nodes cannot exceed a certain number. It is worth noting that these nodes and SSID can also be used as identifiers, which can be used in various devices, including various wireless game consoles, for example, you can use Ad- Use Hoc on PlayStation or Nintendo devices to play simultaneous games with your friends.
It is obvious that the operating frequency of each Ad Hoc network can be different and depending on the type of application, they are used in all kinds of networks, from home networks to military networks and sometimes satellite networks, in many military users of networks Ad Hoc is used to find the location of a device, especially mobile devices that are in the military area and locate them. This kind of wireless network structure can also be used in environmental protection cases. You may have seen in many wildlife documentaries that after an animal is killed, a transmitter is connected to it, which tracks the location of the animal over time. The connection to this device is displayed on the map, all these facilities are among the capabilities that Ad Hoc wireless networks offer us. Using this method, biologists can even observe and record the way of life and the paths that the animal has moved during the maintenance of the Ad Hoc transmitter.
It is called those protocols that continuously update the shape of the network using the information exchange of network nodes. Therefore, at the time of need, the intentions are always clear. The family of distance vector protocols are examples of this type of routing. The first methods that were considered in the discussion of ad hoc network routing were of this type of protocol. The biggest problem that arises while using routing table protocols in ad hoc networks is caused by the continuous change of the network shape. Therefore, network shape information must be published regularly, which creates a heavy cost in resources such as bandwidth, battery power, and processing time.
Also, due to the different patterns that can exist for a network, sometimes only a percentage of routers are used, and the rest publish their information on the network for no reason. However, these protocols can be used for those ad hoc networks whose speed of changes is low enough.
These routing protocols have different methods for disseminating the changed network topology information and the number of necessary routing related tables. Some examples of these protocols are DSDV, CGSR, WRP, FSR, GSR and HSR. In tabular algorithms, there is always a certain number of control information transfers in progress, even if no data transfer is done in the network for a while, it is clear that such a method will bear a lot of cost.
On-demand
routing is one of the latest wireless routing designs that has reached the scalable class, which is based on a question-and-answer policy. Unlike the previous group, nodes in such protocols do not continuously notice the network shape change and the network shape is introduced only to users who intend to use or route. Route discovery is usually done with the route request flow in the network, and the node located in the destination route notifies the arrival of the request by sending the route response to the source node using the reverse link, and when a router is not used in the network. will be removed from the routing table.
When the use of a router in the network is required, a "route request" message is broadcast in the network and this message is received by the source or a nearby node. That node also sends a "route response" message to the primary node. AODV, DSR, TORA, LMR and ABR protocols are examples of necessity protocols and the purpose of these protocols is to minimize the cost by discovering only requested and required routes. This group of protocols will significantly reduce the consumption of network resources and costs, but instead increase the delay when establishing a connection.
In fact, these protocols are used to reduce the slag of maintaining the information of tabular protocols. The slag of route discovery when we have a reverse link grows by O(N+M) and it is O(2N) in unidirectional links. There are different ways to discover paths in Niazi algorithms. Most algorithms use a scheme derived from bridge routing (LAN), i.e. route discovery by reverse learning.

An ad hoc network occurs when two or more computers are connected through an intermediary node. First, ad hoc network does not need basic infrastructure such as routers or access points. Secondly, an ad hoc network is a temporary wireless network. In any place where there is no internet and people need to share their files, ad hoc network...
read more
As you know, the server is a powerful and always-on computer that consists of a series of hardware and software resources and needs settings and maintenance. In fact, by implementing appropriate settings for the server, you can somehow architect its structure and make better use of its resources. In other words, using the server settings...
read more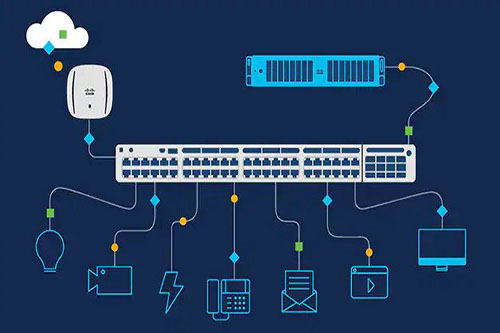
Suppose you are going to set up a computer network. A computer has a port or network card and a place to connect to another system. What if you have several computers in your company or complex that are supposed to communicate with each other? You can communicate with only one other computer from one system. To communicate with several systems, it is necessary to.....
read more